
Fedora Tutorial – Hello Linux users, today we will learn how to secure our web server by enable SSL on Apache Fedora 26. On my previous tutorial, we have learned how to install and configure LAMP Server on Fedora 26. If you follow that guide, it would be easier for you to continue to secure your web server with this tutorial. There are several steps to enable SSL on web server Fedora 26.
Steps to enable SSL on Apache Fedora 26
Step 1. Create Certificate
First, we need to create a new SSL certificate. Log in to the server and execute these commands below.
cd /etc/pki/tls/certs make server.key
Output example
[root@fedora certs]# make server.key umask 77 ; \ /usr/bin/openssl genrsa -aes128 2048 > server.key Generating RSA private key, 2048 bit long modulus .....................................+++ ...+++ e is 65537 (0x010001) Enter pass phrase: Verifying - Enter pass phrase:
Now we need to remove pass phrase from the private key
[root@fedora certs]# openssl rsa -in server.key -out server.key Enter pass phrase for server.key: writing RSA key
Create server.csr
make server.csr
Output Example
[root@fedora certs]# make server.csr umask 77 ; \ /usr/bin/openssl req -utf8 -new -key server.key -out server.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:ID State or Province Name (full name) []:Solo Locality Name (eg, city) [Default City]:Solo Organization Name (eg, company) [Default Company Ltd]:manjaro.site Organizational Unit Name (eg, section) []:IT Common Name (eg, your name or your server's hostname) []:manjaro.site Email Address []:admin@manjaro.site Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: #Press Enter An optional company name []: #Press Enter
Followed by the last command
openssl x509 -in server.csr -out server.crt -req -signkey server.key -days 3650
Output
[root@fedora certs]# openssl x509 -in server.csr -out server.crt -req -signkey server.key -days 3650 Signature ok subject=C = ID, ST = Solo, L = Solo, O = manjaro.site, OU = IT, CN = manjaro.site, emailAddress = admin@manjaro.site Getting Private key
Now we have completed to create SSL certificate.
Step 2. Configure HTTPD for SSL
Install mod_ssl
dnf install mod_ssl
Output
[root@fedora certs]# dnf install mod_ssl Last metadata expiration check: 1:09:44 ago on Wed 23 Aug 2017 06:45:11 AM WIB. Dependencies resolved. ========================================================================================================================================== Package Arch Version Repository Size ========================================================================================================================================== Installing: mod_ssl x86_64 1:2.4.27-2.fc26 updates 113 k Transaction Summary ========================================================================================================================================== Install 1 Package Total download size: 113 k Installed size: 232 k Is this ok [y/N]:
Edit /etc/httpd/conf.d/ssl.conf
nano /etc/httpd/conf.d/ssl.conf
Now find and uncomment line 59 and 60 and change them to the following. Off course you need to modify the server name with your own.
DocumentRoot "/var/www/html" ServerName www.manjaro.site:443
On Line 76 and 77, change them to:
SSLProtocol -all +TLSv1 +TLSv1.1 +TLSv1.2 SSLProxyProtocol -all +TLSv1 +TLSv1.1 +TLSv1.2
On line 98 change to the following
SSLCertificateFile /etc/pki/tls/certs/server.crt
Also on line 105 change it to the following
SSLCertificateKeyFile /etc/pki/tls/certs/server.key
Close and save the file. Finally restart httpd
systemctl restart httpd
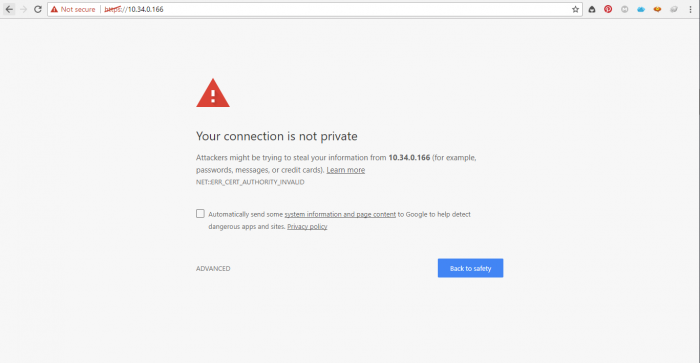
Now try accessing the web server using https
https://ip-server
You will see such error above. It is normal since we use self signed certificate on the system. Thank you for reading this post on How to enable SSL on Apache Fedora 26. See you on the next tutorial.
Thanks
On fedora 29 i get the following:
[root@localhost ~]# cd /etc/pki/tls/certs
[root@localhost certs]# make server.key
make: *** No rule to make target ‘server.key’. Stop.
[root@localhost certs]# ls
ca-bundle.crt ca-bundle.trust.crt